In light of recent events regarding Solorigate (the supply-chain attack on Solarwinds software Orion) many are looking to improve security in their Azure AD environment. Me as an Identity and Security Architect has been following the topic with great interest as well as assisting and providing feedback.
CrowdStrike has release their own tool on GitHub in order to help organizations like yours to Audit Azure AD in order to hopefully stay one step ahead of the perpetrators.
The tool can be found at https://github.com/CrowdStrike/CRT and provides an in depth analysis of your Azure AD Tenant in order to further improve the security posture such as:
Exchange Online (O365):
Federation Configuration
Federation Trust
Client Access Settings Configured on Mailboxes
Mail Forwarding Rules for Remote Domains
Mailbox SMTP Forwarding Rules
Delegates with 'Full Access' Permission Granted
Delegates with Any Permissions Granted
Delegates with 'Send As' or 'SendOnBehalf' Permissions
Exchange Online PowerShell Enabled Users
Users with 'Audit Bypass' Enabled
Mailboxes Hidden from the Global Address List (GAL)Azure AD:
Service Principal Objects with KeyCredentials
O365 Admin Groups Report
Delegated Permissions & Application PermissionsThere are some pre-reqs however, you of course need the appropriate Powershell modules (which the script will download and install for you if needed) and in order to get the report in full extent you need to run it as a Global Administrator.
This tool in combination of best practices regarding Conditional Access, Identity Lifecycle Management and Privileged Access Management will for sure help you on your journey to solidify the security posture of your Azure AD.
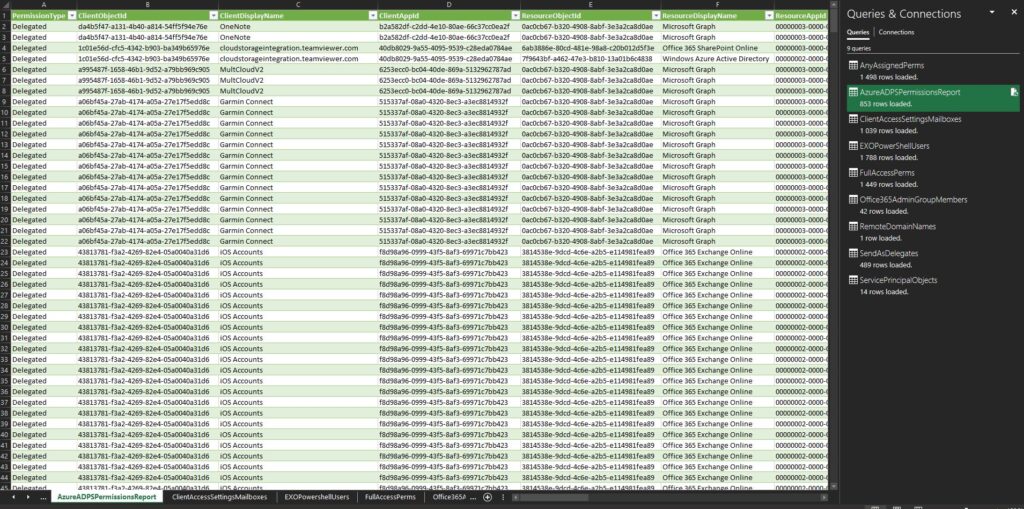
Given that you´ve performed an export successfully, you can then use Excel to import the .csv files provided by the script in order to furhter investigate and take action on points neccessary: